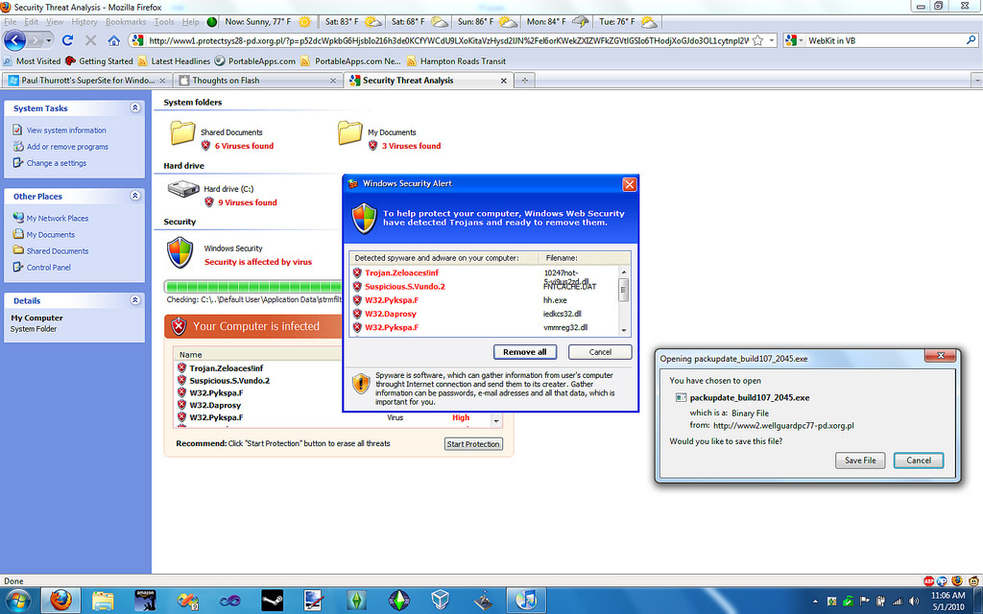
Fake Antivirus and the Rouge Security Software Problem
Rogue security software (aka fake antivirus programs) is a form of malicious software and Internet fraud that misleads users into believing there is a virus on their computer, and manipulates them into paying money for a fake malware removal tool (that actually introduces malware to the computer). It is a form of scareware that manipulates users through fear, and a form of ransomware.Rogue security software has become a serious security threat in desktop computing since 2008.
Rogue security software mainly relies on social engineering (fraud) to defeat the security built into modern operating system and browser software and install itself onto victims’ computers. A website may, for example, display a fictitious warning dialog stating that someone’s machine is infected with a computer virus, and encourage them through manipulation to install or purchase scareware in the belief that they are purchasing genuine antivirus software.
Most have a Trojan horse component, which users are misled into installing. The Trojan may be disguised as:
A browser plug-in or extension (typically toolbar)
An image, screensaver or archive file attached to an e-mail message
Multimedia codec required to play a certain video clip
Software shared on peer-to-peer networks
A free online malware-scanning service
Some rogue security software, however, propagate onto users’ computers as drive-by downloads which exploit security vulnerabilities in web browsers, PDF viewers, or email clients to install themselves without any manual interaction.
More recently, malware distributors have been utilizing SEO poisoning techniques by pushing infected URLs to the top of search engine results about recent news events. People looking for articles on such events on a search engine may encounter results that, upon being clicked, are instead redirected through a series of sites before arriving at a landing page that says that their machine is infected and pushes a download to a “trial” of the rogue program. A 2010 study by Google found 11,000 domains hosting fake anti-virus software, accounting for 50% of all malware delivered via internet advertising.
Cold-calling has also become a vector for distribution of this type of malware, with callers often claiming to be from “Microsoft Support” or another legitimate organization.
Common ways user gets infected
Black Hat SEO
Black Hat search engine optimization (SEO) is a technique used to trick search engines like Google and Yahoo into displaying malicious URLs in search results. The malicious webpages are filled with popular keywords in order to achieve a higher ranking in the search results. When the end user searches the web, one of these infected webpages is returned. Usually the most popular keywords from services such as Google Trends are used to generate webpages via PHP scripts placed on the compromised website. These PHP scripts will then monitor for search engine crawlers and feed them with specially crafted webpages that are then listed in the search results. Then, when the user searches for their keyword or images and clicks on the malicious link, they will be redirected to the Rogue security software payload.
Malvertising
Most websites usually employ third-party services for advertising on their webpages. If one of these advertising services is compromised, they may end up inadvertently infecting all of the websites using their service by advertising rogue security software.
Spam campaigns
Spam messages that include malicious attachments, links to binaries and drive-by download sites are another common mechanism for distributing rogue security software. Spam emails are often sent with content associated with typical day-to-day activities such as parcel deliveries, or taxation documents, designed to entice users to click on links or run attachments. When users succumb to these kinds of social engineering tricks they are quickly infected either directly via the attachment, or indirectly via a malicious website. This is known as a drive-by download. Usually in drive-by download attacks the malware is installed on the victim’s machine without any interaction or awareness and occurs simply by visiting the website.
Once installed, the rogue security software may then attempt to entice the user into purchasing a service or additional software by:
Alerting the user with the fake or simulated detection of malware or pornography.
Displaying an animation simulating a system crash and reboot.
Selectively disabling parts of the system to prevent the user from uninstalling the malware. Some may also prevent anti-malware programs from running, disable automatic system software updates and block access to websites of anti-malware vendors.
Installing actual malware onto the computer, then alerting the user after “detecting” them. This method is less common as the malware is likely to be detected by legitimate anti-malware programs.
Altering system registries and security settings, then “alerting” the user.
What do I do if I get one of these on my computer?
The most important thing to remember is to never give away any password information or any type of bank details. NEVER pay them to remove the program from your computer.
Try installing free programs like malware bytes and run the scan. If you are unable to install anything or even get to the internet it may be time to call a professional.
Source: Wikipedia